The Data Don't Lie
But politicians do.
As many of you likely noticed, the Miami Herald last week published an in-depth digital article on Ariel’s phishing scandal—one that earned front-page placement in Monday’s print edition. As someone who has routinely taken the Herald to task for its peculiar aversion to stories that might prove helpful to its bête noire, Mayor Lago (or harmful to his adversaries, because politics is all too often a zero-sum game), I felt genuine relief, even gratitude, at what was a long-overdue restoration of at least some semblance of balance and objectivity. Nevertheless, I should probably resist lavishing too much praise on the Herald for actually doing the one thing it’s supposed to do, lest I become the kind of “low expectation having motherfu**er” Chris Rock brilliantly took to task here:
But I will tip my hat to reporter Michelle Marchante, who produced a particularly fine specimen of thoughtful, thorough, and balanced local journalism—something that proved elusive to Marchante’s predecessor, Tsk Tsk Tess Riski, now a named defendant in David and Leila Center’s $885 million defamation lawsuit against the Herald. Marchante consulted technical experts, gave all parties an opportunity to respond, and made a genuine effort to grapple with a relatively complex scandal in a way that would be accessible to lay readers. It’s the kind of serious, procedural journalism this story deserves.
That said, there’s one technical aspect that merits clarification, as it has the potential to create confusion about just how conclusive the evidence against Ariel actually is. I’m referring specifically to the question of attribution, i.e. whether we can definitively prove that Ariel himself was behind the PeopleCountUSA Mailchimp accounts. The article seems to suggest that despite mountains of circumstantial evidence, the only technical connection to Ariel is that americanaresearch.com (the email domain used to register one of the Mailchimp accounts) redirects to marketseur.com, a site owned and operated by Ariel.
To her credit, Marchante didn’t phone it in. She consulted Stuart Madnick, a professor of information technology at MIT’s Sloan School of Management. Here’s the relevant passage (emphasis mine):
The americanaresearch.com URL redirects to Marketseur, a company registered to The American Strategies Group. Fernandez is president of Marketseur and The American Strategies Group, records show.
It’s worth noting that anyone can buy a URL and redirect it to another website, according to Stuart Madnick, a professor of information technology at MIT Sloan School of Management. He compares it to how people can set up phone numbers to forward to another number.
“You don’t have to have control of both sites to do that,” Madnick said.
This is absolutely correct…as far as it goes. Anyone can indeed redirect a URL they control to one they don’t. It happens all the time.
The problem is that’s not what happened here.
This is the one and only knock I have on Marchante’s execution. She enlisted an expert but either didn’t provide him with the complete technical data or didn’t insist he engage with it. The result is an expert opinion that, while technically accurate in the abstract, amounts to an irrelevant generality that doesn’t address the actual evidence at hand.
By the way, I happen to know Professor Madnick didn’t engage with the technical data because he told me so himself. Shortly after the article was published, I reached out offering him the opportunity to review the forensic analysis. He graciously replied, confirming he had “not studied the details of the case” and had merely answered “is it possible type questions.” He ultimately declined to review the data, citing personal matters requiring his attention. Out of respect for that private exchange, I won’t share screenshots of our correspondence publicly, though I would, of course, provide them to investigators upon request.
In any event, everything Professor Madnick needed to reach a more definitive assessment was laid out in my June 25th post, “The Phisher King.” Had he reviewed the featured technical analysis or even performed a DNS check himself, he would have been able to rule out an external redirect as a plausible explanation.
The evidence
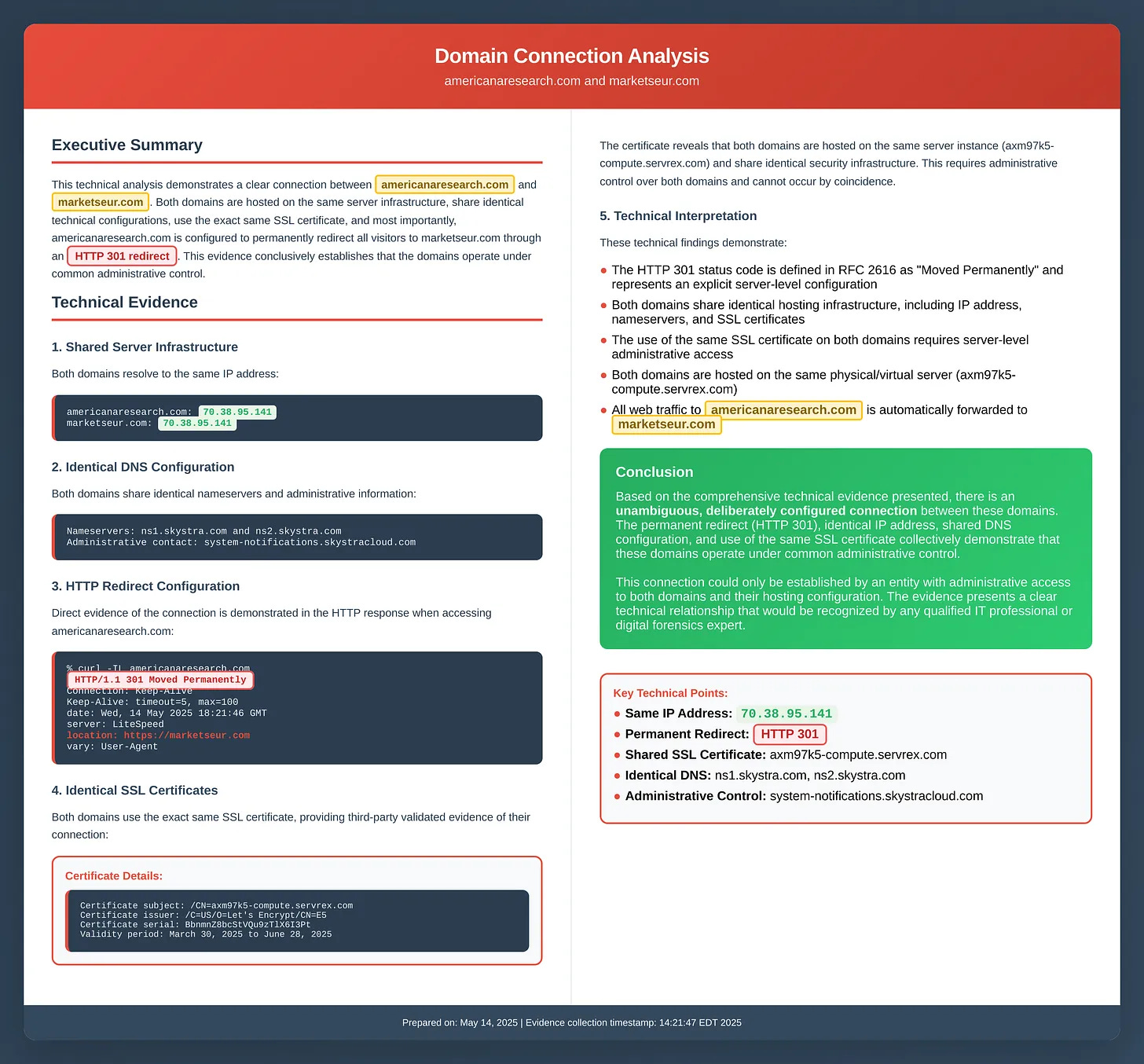
The redirect from americanaresearch.com to marketseur.com (which appears to have finally been disabled in recent days) wasn’t a simple external redirect that anyone could configure by purchasing a domain and pointing it elsewhere. It was an HTTP 301 redirect, or what’s known in technical parlance as a “server-side” redirect. See the exhibit below, which I pulled from “The Phisher King:”
This is a critical distinction. A server-side redirect means the forwarding was configured internally, within the hosting environment itself, by someone with administrative access to the server where both domains are hosted. You can’t create this type of redirect externally by just buying a domain and tweaking DNS settings. No siree. You need to be logged into the actual hosting control panel.
Moreover, the redirect is only half the story. The evidence shows that americanaresearch.com and marketseur.com didn’t merely redirect to each other but rather shared the same fundamental infrastructure. Here, specifically, is the overlap:
Same IP Address: Both domains resolve to 70.38.95.141. This means they’re hosted on the same physical or virtual server.
Same SSL Certificate: Both domains use the identical security certificate (serial number: BbnmnZ8bcStVQu9zTlX6I3Pt), issued to axm97k5-compute.servrex.com. For two domains to share the same SSL certificate requires server-level administrative configuration. You can’t fake this, spoof it, or manipulate it externally.
Same Nameservers: Both domains are managed through ns1.skystra.com and ns2.skystra.com, indicating they’re administered through the same DNS infrastructure and hosting account. Note, these exact nameservers are also associated with voteariel.com and betteryouminute.com, both of which belong or belonged to Ariel.
Same Server Instance: Both domains are hosted on the identical server (axm97k5-compute.servrex.com), as confirmed by the SSL certificate data.
In other words, the external redirect hypothesis is dead in the water. This degree of overlap can only be achieved from within, which leaves us with two distinct possibilities:
Ariel was hacked by an extraordinarily sophisticated operator who managed to gain admin access to both his domain registrar and his hosting provider, which is no small feat, given that these are independent, professionally maintained systems with their own security protocols. This hacker then maintained that access undetected for months, possibly years. And having achieved this level of penetration, this mastermind with CIA/Mossad hacking abilities decided the optimal use of that access would be to, um, engineer an elaborate frame-up of a no-name local politician involving fake polling organizations, tracking links, and Mailchimp accounts that would require months of detective work to uncover and even longer to explain to anyone who isn’t a digital forensics expert.
Never mind that a hacker with this level of access could have simply defaced Ariel’s campaign website with embarrassing content. Or planted obviously fraudulent donor records that would trigger an immediate FEC investigation. Or stolen constituent data and dumped it publicly. Or modified his site to serve malware. Or held his domains for ransom. Or done literally anything that would cause immediate, obvious, and irreparable damage while being infinitely easier to execute and explain.
No, this hypothetical hacker instead chose to go with the Rube Goldberg machine of cybercrimes by engineering an impossibly convoluted scheme that would only come to light if a determined resident filed a John Doe lawsuit, successfully subpoenaed Mailchimp, obtained technical records, and shared them with an anonymous blogger whom he could rely upon to perform a forensic analysis sophisticated enough to trace domain redirects and SSL certificates.
Ariel actually is the culprit and is, get this, lying like the pathological liar he has proven himself to be time and time again.
Gee, I don’t know, it’s almost impossible to decide which is more plausible. 🤦♀️
A dumb denial
The most surprising thing about the Herald article—besides the fact that it was written at all—is Ariel’s explicit denial of what his attorney, David Winker, characterized as “baseless and politically motivated allegations.” The plural is key there. Ariel is denying all the allegations, which necessarily includes the most fundamental one: that he was behind the surveys in the first place.
As you can probably tell from the subheader, I think this is a spectacularly dumb move on Ariel’s part, and for a couple of reasons. First, deliberate deception is one of the primary transgressions here. Assuming Ariel really was behind this, misleading the public with false names, fake entities, and fraudulent pretenses through the surveys themselves was only the beginning of the lie. The lie doesn’t end when the surveys stop, rather it continues and compounds with every subsequent denial. Going on to consistently deny involvement after there’s more than reasonable suspicion to believe he’s the culprit perpetuates the deception. It’s an ongoing transgression, one that he aggravates every time he rejects an opportunity to come clean. In other words, it would appear Ariel has violated Healy’s first law of holes.
The second reason denial is such a poor strategy is that it tragically underestimates the weight and quality of the technical evidence pointing directly at Ariel. Granted, we just witnessed an intelligent and diligent professional journalist with direct access to an MIT expert misunderstand the evidence, but that was due to incomplete information and context. Ariel has no such excuse. He should know better. He should understand that because americanaresearch.com used a server-side redirect to Marketseur and shares identical infrastructure with it, the only way anyone other than him could have orchestrated this scheme is if someone gained unauthorized access to his hosting account through the kind of fantastical hack I described above. And we can rule out disgruntled employees with admin access because, well, Ariel doesn’t have employees.
And that’s what this really boils down to. When you combine Ariel’s denial with the fact that the redirect was executed internally, it leaves ‘he was hacked’ as the only possible, albeit highly implausible, alternative theory. Fortunately, that theory happens to be eminently falsifiable, especially if Ariel cooperates.
When someone logs into a hosting account, the system automatically records that access. Every login generates a log entry showing the timestamp, the IP address used, and often the geographic location associated with that IP. These access logs are standard practice for hosting providers and are retained for extended periods. If Ariel’s Skystra hosting account was truly compromised by a sophisticated hacker in July or August of 2023, those logs would show unauthorized access from unfamiliar IP addresses, likely from locations Ariel has never been. The evidence would be right there in black and white.
Similarly, domain registrars maintain logs of all administrative actions taken on domains. If someone accessed Ariel’s registrar account to purchase americanaresearch.com and peoplecountusa.com, those logs would show it. If someone configured DNS settings or nameservers, the logs would capture that too. This is by no means speculative. These records definitely exist, and Ariel has every right to access and share them.
To state it plainly, if Commissioner Fernandez was truly hacked, he should prove it—not to mention the fact he should have known it, as there would have been numerous emailed warnings that his accounts were being accessed from new locations, password reset notifications, and purchase confirmations for domains. He should contact Skystra and his domain registrar, request his complete account access logs for July through December 2023, authorize their release to investigators, and allow an independent forensic examiner to review them. If those logs show unauthorized access from IP addresses he can’t account for, he’ll be vindicated. The investigation will shift immediately to identifying the perpetrator who framed him, and he’ll have every right to sue that person for everything they’ve got.
But if he refuses to provide these logs, or if he claims they’ve been deleted or are unavailable, or if he simply continues to ignore this straightforward path to exoneration, then reasonable people can draw only one conclusion. Because let’s face it, no innocent person who’s been falsely accused of a potential crime and who has easy access to evidence that would prove his innocence sits on that evidence. They produce it. Immediately. Enthusiastically.
In sum, Ariel’s blanket denial combined with the technical evidence illuminates a clear path toward the truth. And if the truth is exonerating, then helping investigators navigate that path should be Ariel’s top priority. Should he choose obstruction instead, well, that will tell us everything we need to know and, let’s face it, what we already know.


Thank you once again Aesop for bringing the truth to light.
Great example on high moralist politicians who turn to be fraudsters. The more virtuous, high moral, selfness there is in the self portrayal, the higher chances that that the person is a sneaky scammer. This is common in banana republics: the anti drug czar who is running the cartel, or the anti-corruption minister who runs kick-backs operations. Ariel could have a great future in a banana republic. But here at Coral Gables, we had enough.